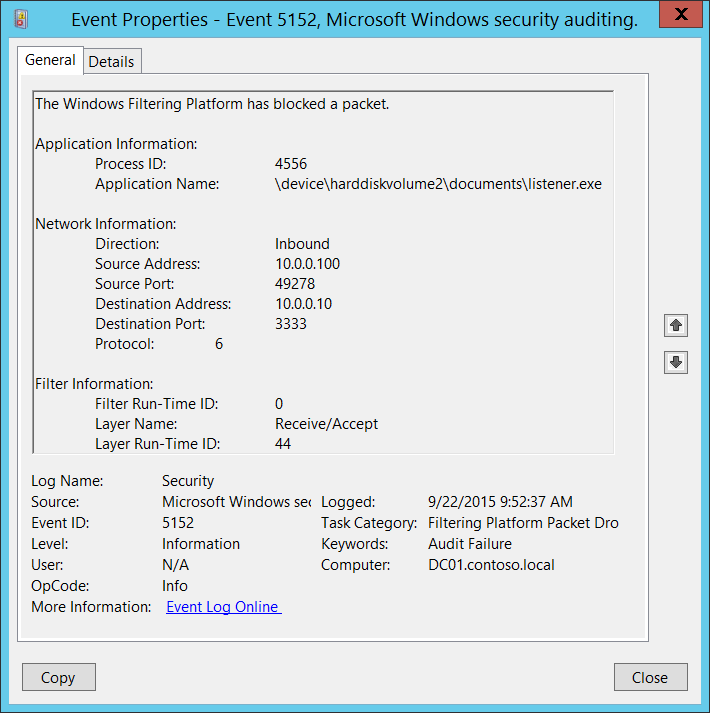
5152(F): The Windows Filtering Platform blocked a packet.
Applies to
- Windows 10
- Windows Server 2016
Event Description:
This event generates when Windows Filtering Platform has blocked a network packet.
This event is generated for every received network packet.
NoteВ В For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
Required Server Roles: None.
Minimum OS Version: Windows Server 2008, Windows Vista.
Event Versions: 0.
Field Descriptions:
Application Information:
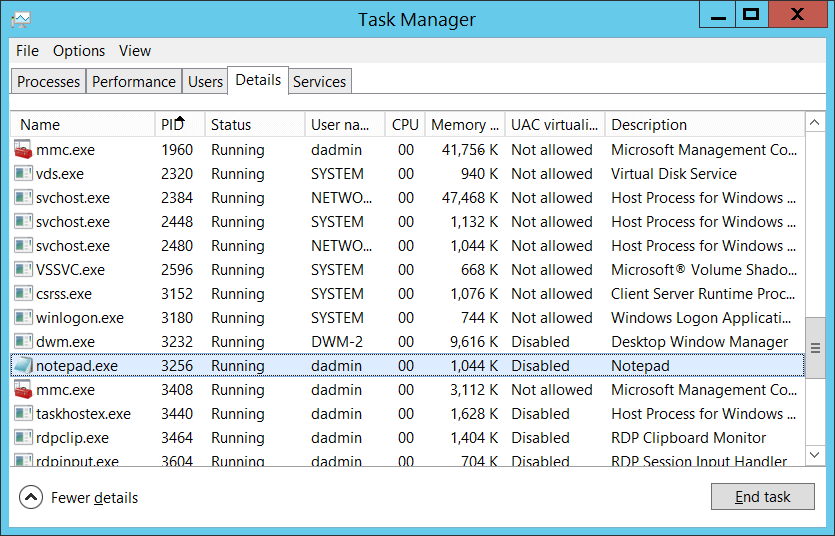
Process ID [Type = Pointer]: hexadecimal Process ID of the process to which blocked network packet was sent. Process ID (PID) is a number used by the operating system to uniquely identify an active process. To see the PID for a specific process you can, for example, use Task Manager (Details tab, PID column):
If you convert the hexadecimal value to decimal, you can compare it to the values in Task Manager.
You can also correlate this process ID with a process ID in other events, for example, “4688: A new process has been created” Process Information\New Process ID.
Application Name [Type = UnicodeString]: full path and the name of the executable for the process.
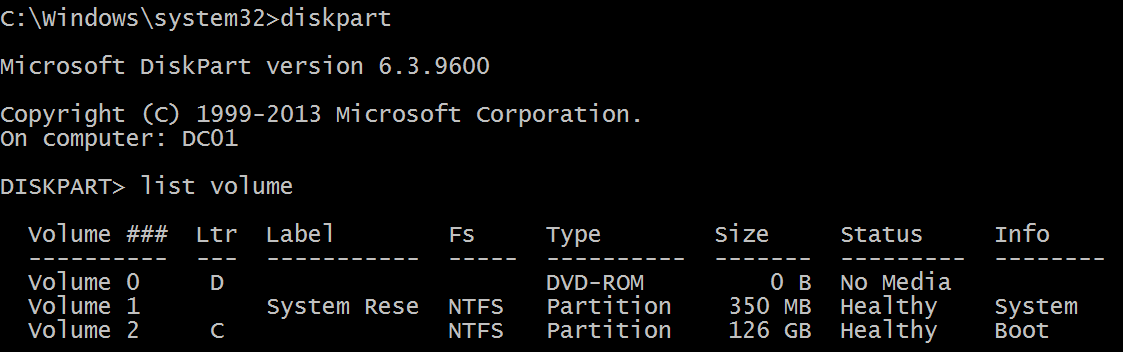
Logical disk is displayed in format \device\harddiskvolume#. You can get all local volume numbers by using diskpart utility. The command to get volume numbers using diskpart is “list volume”:
Network Information:
Direction [Type = UnicodeString]: direction of blocked connection.
Inbound – for inbound connections.
Outbound – for unbound connections.
Source Address [Type = UnicodeString]: local IP address on which application received the packet.
:: — all IP addresses in IPv6 format
0.0.0.0 — all IP addresses in IPv4 format
127.0.0.1 , ::1 — localhost
Source Port [Type = UnicodeString]: port number on which application received the packet.
Destination Address [Type = UnicodeString]: IP address from which packet was received or initiated.
:: — all IP addresses in IPv6 format
0.0.0.0 — all IP addresses in IPv4 format
127.0.0.1 , ::1 — localhost
Destination Port [Type = UnicodeString]: port number which was used from remote machine to send the packet.
Protocol [Type = UInt32]: number of protocol which was used.
| Service | Protocol Number |
|---|---|
| Internet Control Message Protocol (ICMP) | 1 |
| Transmission Control Protocol (TCP) | 6 |
| User Datagram Protocol (UDP) | 17 |
| General Routing Encapsulation (PPTP data over GRE) | 47 |
| Authentication Header (AH) IPSec | 51 |
| Encapsulation Security Payload (ESP) IPSec | 50 |
| Exterior Gateway Protocol (EGP) | 8 |
| Gateway-Gateway Protocol (GGP) | 3 |
| Host Monitoring Protocol (HMP) | 20 |
| Internet Group Management Protocol (IGMP) | 88 |
| MIT Remote Virtual Disk (RVD) | 66 |
| OSPF Open Shortest Path First | 89 |
| PARC Universal Packet Protocol (PUP) | 12 |
| Reliable Datagram Protocol (RDP) | 27 |
| Reservation Protocol (RSVP) QoS | 46 |
Filter Information:
Filter Run-Time ID [Type = UInt64]: unique filter ID which blocked the packet.
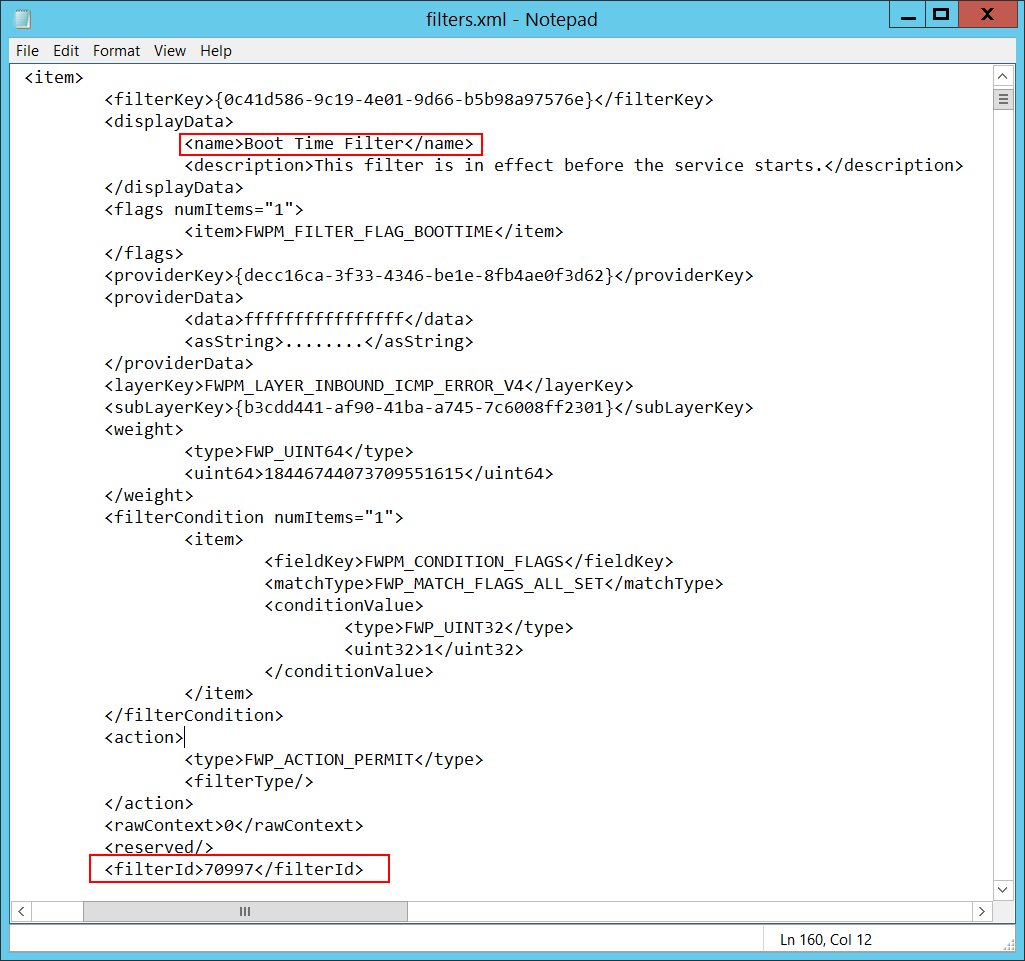
To find specific Windows Filtering Platform filter by ID you need to execute the following command: netsh wfp show filters. As result of this command filters.xml file will be generated. You need to open this file and find specific substring with required filter ID ( ), for example:
Layer Name [Type = UnicodeString]: Application Layer Enforcement layer name.
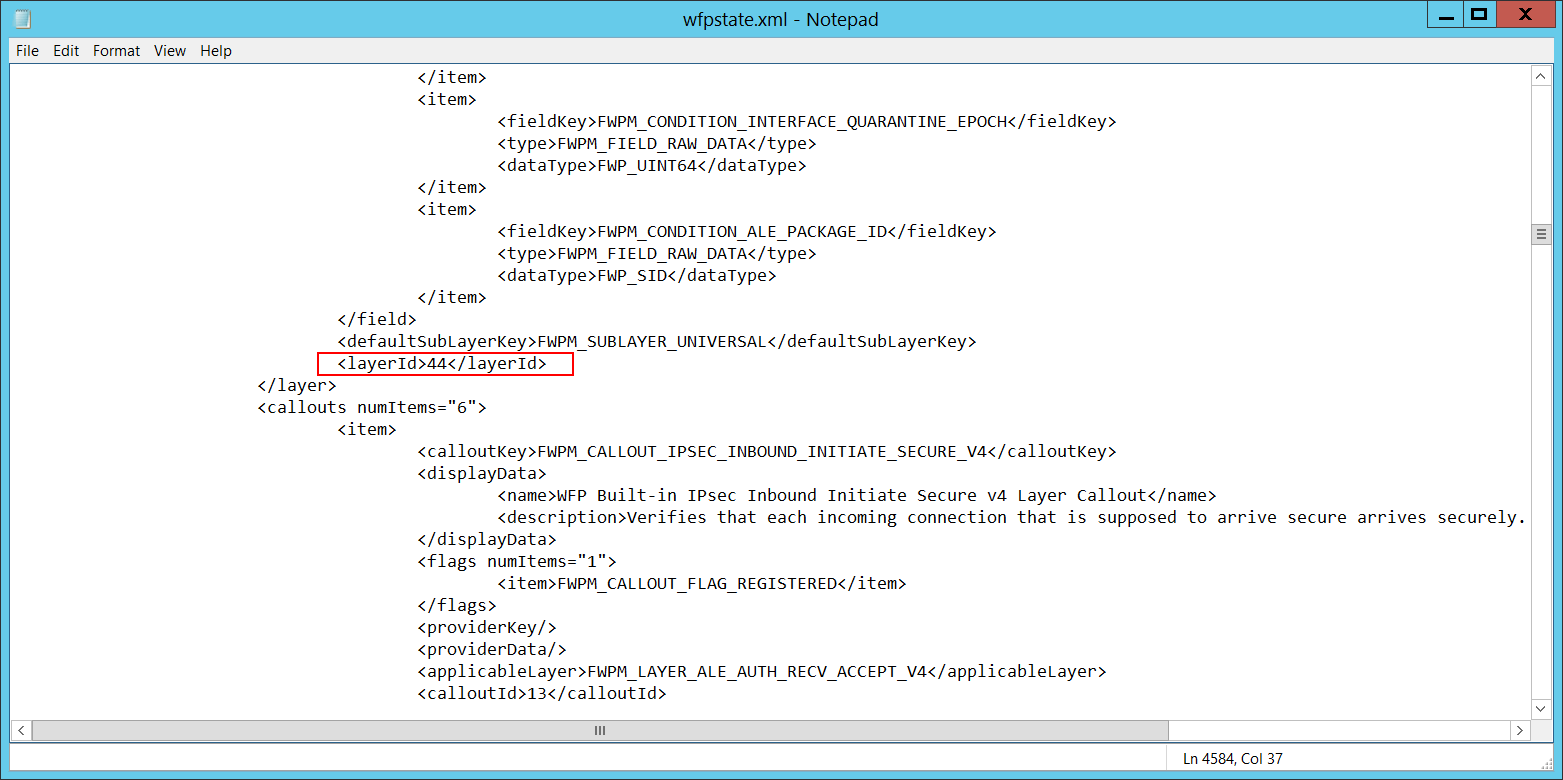
Layer Run-Time ID [Type = UInt64]: Windows Filtering Platform layer identifier. To find specific Windows Filtering Platform layer ID you need to execute the following command: netsh wfp show state. As result of this command wfpstate.xml file will be generated. You need to open this file and find specific substring with required layer ID ( ), for example:
Security Monitoring Recommendations
For 5152(F): The Windows Filtering Platform blocked a packet.
If you have a pre-defined application which should be used to perform the operation that was reported by this event, monitor events with “Application” not equal to your defined application.
You can monitor to see if “Application” is not in a standard folder (for example, not in System32 or Program Files) or is in a restricted folder (for example, Temporary Internet Files).
If you have a pre-defined list of restricted substrings or words in application names (for example, “mimikatz” or “cain.exe”), check for these substrings in “Application.”
Check that Source Address is one of the addresses assigned to the computer.
If the computer or device should not have access to the Internet, or contains only applications that don’t connect to the Internet, monitor for 5152 events where Destination Address is an IP address from the Internet (not from private IP ranges).
If you know that the computer should never contact or be contacted by certain network IP addresses, monitor for these addresses in “Destination Address.”
If you have an allow list of IP addresses that the computer or device is expected to contact or be contacted by, monitor for IP addresses in “Destination Address” that are not in the allow list.
If you need to monitor all inbound connections to a specific local port, monitor for 5152 events with that “Source Port.”
Monitor for all connections with a “Protocol Number” that is not typical for this device or compter, for example, anything other than 1, 6, or 17.
If the computer’s communication with “Destination Address” should always use a specific “Destination Port,” monitor for any other “Destination Port.”
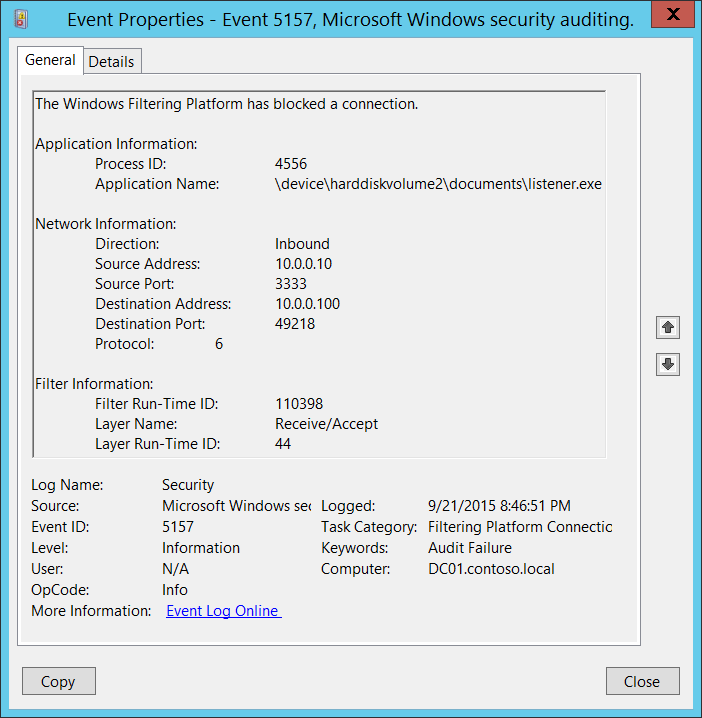
5157(F): The Windows Filtering Platform has blocked a connection.
Applies to
- Windows 10
- Windows Server 2016
Event Description:
This event generates when Windows Filtering Platform has blocked a connection.
NoteВ В For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
Required Server Roles: None.
Minimum OS Version: Windows Server 2008, Windows Vista.
Event Versions: 0.
Field Descriptions:
Application Information:
Process ID [Type = Pointer]: hexadecimal Process ID of the process that attempted to create the connection. Process ID (PID) is a number used by the operating system to uniquely identify an active process. To see the PID for a specific process you can, for example, use Task Manager (Details tab, PID column):
If you convert the hexadecimal value to decimal, you can compare it to the values in Task Manager.
You can also correlate this process ID with a process ID in other events, for example, “4688: A new process has been created” Process Information\New Process ID.
Application Name [Type = UnicodeString]: full path and the name of the executable for the process.
Logical disk is displayed in format \device\harddiskvolume#. You can get all local volume numbers by using diskpart utility. The command to get volume numbers using diskpart is “list volume”:
Network Information:
Direction [Type = UnicodeString]: direction of blocked connection.
Inbound – for inbound connections.
Outbound – for unbound connections.
Source Address [Type = UnicodeString]: local IP address on which application received the connection.
:: — all IP addresses in IPv6 format
0.0.0.0 — all IP addresses in IPv4 format
127.0.0.1 , ::1 — localhost
Source Port [Type = UnicodeString]: port number on which application received the connection.
Destination Address [Type = UnicodeString]: IP address from which connection was received or initiated.
:: — all IP addresses in IPv6 format
0.0.0.0 — all IP addresses in IPv4 format
127.0.0.1 , ::1 — localhost
Destination Port [Type = UnicodeString]: port number which was used from remote machine to initiate connection.
Protocol [Type = UInt32]: number of protocol which was used.
| Service | Protocol Number |
|---|---|
| Internet Control Message Protocol (ICMP) | 1 |
| Transmission Control Protocol (TCP) | 6 |
| User Datagram Protocol (UDP) | 17 |
| General Routing Encapsulation (PPTP data over GRE) | 47 |
| Authentication Header (AH) IPSec | 51 |
| Encapsulation Security Payload (ESP) IPSec | 50 |
| Exterior Gateway Protocol (EGP) | 8 |
| Gateway-Gateway Protocol (GGP) | 3 |
| Host Monitoring Protocol (HMP) | 20 |
| Internet Group Management Protocol (IGMP) | 88 |
| MIT Remote Virtual Disk (RVD) | 66 |
| OSPF Open Shortest Path First | 89 |
| PARC Universal Packet Protocol (PUP) | 12 |
| Reliable Datagram Protocol (RDP) | 27 |
| Reservation Protocol (RSVP) QoS | 46 |
Filter Information:
Filter Run-Time ID [Type = UInt64]: unique filter ID which blocked the connection.
To find specific Windows Filtering Platform filter by ID you need to execute the following command: netsh wfp show filters. As result of this command filters.xml file will be generated. You need to open this file and find specific substring with required filter ID ( ), for example:
Layer Name [Type = UnicodeString]: Application Layer Enforcement layer name.
Layer Run-Time ID [Type = UInt64]: Windows Filtering Platform layer identifier. To find specific Windows Filtering Platform layer ID you need to execute the following command: netsh wfp show state. As result of this command wfpstate.xml file will be generated. You need to open this file and find specific substring with required layer ID ( ), for example:
Security Monitoring Recommendations
For 5157(F): The Windows Filtering Platform has blocked a connection.
If you have a pre-defined application which should be used to perform the operation that was reported by this event, monitor events with “Application” not equal to your defined application.
You can monitor to see if “Application” is not in a standard folder (for example, not in System32 or Program Files) or is in a restricted folder (for example, Temporary Internet Files).
If you have a pre-defined list of restricted substrings or words in application names (for example, “mimikatz” or “cain.exe”), check for these substrings in “Application.”
Check that “Source Address” is one of the addresses assigned to the computer.
If the` computer or device should not have access to the Internet, or contains only applications that don’t connect to the Internet, monitor for 5157 events where “Destination Address” is an IP address from the Internet (not from private IP ranges).
If you know that the computer should never contact or be contacted by certain network IP addresses, monitor for these addresses in “Destination Address.”
If you have an allow list of IP addresses that the computer or device is expected to contact or be contacted by, monitor for IP addresses in “Destination Address” that are not in the allow list.
If you need to monitor all inbound connections to a specific local port, monitor for 5157 events with that “Source Port.”
Monitor for all connections with a “Protocol Number” that is not typical for this device or compter, for example, anything other than 1, 6, or 17.
If the computer’s communication with “Destination Address” should always use a specific “Destination Port,” monitor for any other “Destination Port.”